TeamViewer allows you to see another person’s desktop and control their computer through a secure, encrypted connection that is easy to setup and use. There is no risk associated with using it, as only those who you give the randomly generated user ID and password can connect. You must also “ok” the connection.
It’s very safe, and I have used it to connect to my parents’ computers back home and to a friend’s computer, who lives in Nova Scotia.
Important note: while it allows someone to see and control your computer, you see exactly what they are doing and can type and use the mouse the same as you’ve always done.
To install TeamViewer, go to www.teamviewer.com, click on the ‘download’


under ‘full version’, click the button next to the Windows icon.
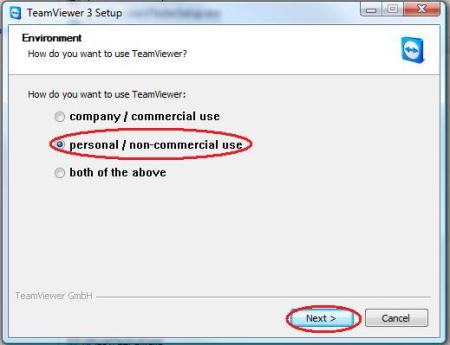
Double click the file you downloaded, and this screen will show up. Click ‘personal/non-commercial use’, and click ‘next.’

Be sure to click box checkboxes to accept the license agreement and to confirm the fact you’ll Only use the program for personal use.
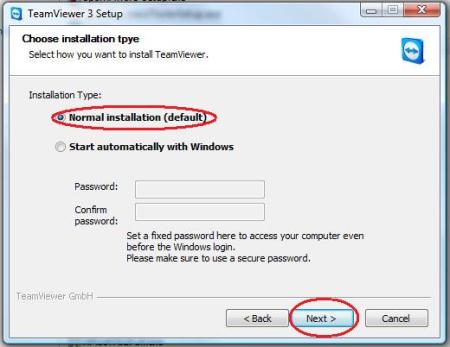
Click “normal installation”. There’s no need for TeamViewer to start when you log into Windows, so don’t Select that.

The program will quickly install, then click “finish” to complete the installation.
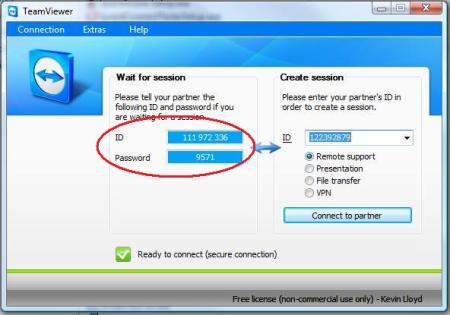
You will then see this screen every time the program starts. When someone (me) attempts to connect to your computer, simply provide the ID and Password under “Wait for session”. You should then be asked to confirm the connection. If not, that’s fine, it’s secure either way.
The ID and password and automatically generated each time the program starts, so noone can access your computer without that information or approval.



 Posted by techqa
Posted by techqa